Wireless Network Security Design Guide
A comprehensive enterprise-grade reference for designing, deploying, and operating secure wireless networks. Covering Zero Trust access, WPA3-Enterprise authentication, network segmentation, WIDS/WIPS, and full lifecycle operations for 500–5,000 concurrent Wi-Fi clients.
System Overview
Wireless network security design aims to reduce unauthorized access, eavesdropping, credential theft, rogue infrastructure, and lateral movement by combining identity-centered access control, air-interface and link encryption, network segmentation and isolation, and continuous monitoring with full auditability. The scope covers enterprise Wi-Fi for staff, IoT, and guests; wireless management plane protection; and operational processes including certificate lifecycle, firmware patching, and incident response.
The design targets organizations deploying 20–300 access points across office floors, semi-public areas, and campus environments, supporting 500–5,000 concurrent Wi-Fi clients. The security baseline follows Zero Trust principles: identity-based access, least privilege, micro-segmentation, and continuous monitoring. Primary authentication uses WPA3-Enterprise (802.1X) with EAP-TLS certificates for managed staff devices, with controlled fallback for legacy endpoints.
Key inputs include business roles (employee, contractor, guest, IoT), device inventory and capabilities, compliance requirements, RF site survey results, and existing IAM, PKI, MDM, and NAC tooling. Outputs include WLAN SSID and role design, RADIUS and NAC policy sets, VLAN and VRF mapping, firewall rules, WIDS and WIPS alerting playbooks, configuration baselines, acceptance test plans, and O&M procedures. Core value is a Wi-Fi environment that is controlled (who, what, where), confidential (encrypted), contained (segmented), and auditable (logged and monitored).
System Architecture
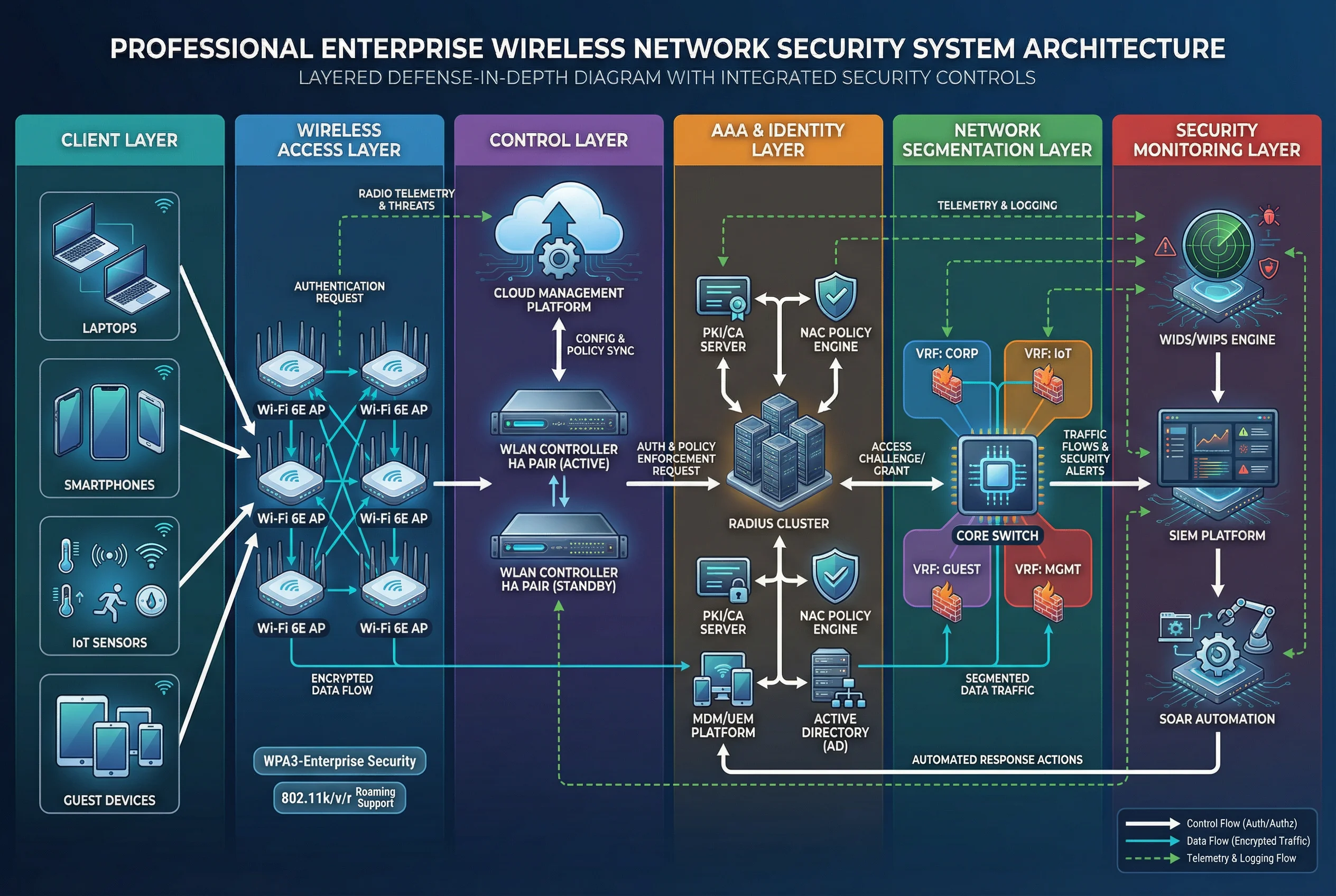
The overall wireless security architecture spans six functional layers, from client endpoints through wireless access, centralized control, identity and AAA services, network segmentation, and security monitoring. Control flows (authentication and authorization) are shown with bold arrows; data flows (business traffic) with thin arrows; and telemetry and logging flows with dashed arrows. This layered model ensures that every access decision is identity-driven, every data path is encrypted and segmented, and every event is logged for audit and detection.
Main Functions
The wireless security platform integrates eight core functional modules, all orchestrated through a central Wireless Security Controller. Each module enforces a specific security dimension — from identity authentication and endpoint compliance through dynamic authorization, network segmentation, encryption lifecycle management, wireless threat detection, logging and audit, and configuration baseline management. Policy decisions flow outward from the controller to enforcement points, while telemetry flows inward to the SIEM for correlation and alerting.

| Function | Description | Acceptance Criteria |
|---|---|---|
| 802.1X / EAP-TLS Authentication | Strong identity assurance via certificate-based mutual authentication; eliminates shared credential risk | Certificate validation and revocation behavior verified under load |
| Role-Based Authorization (Dynamic VLAN/ACL) | Least privilege per user and device type; RADIUS returns role attributes enforced by AP and switch | Correct role mapping and isolation tests pass for all defined roles |
| NAC Posture & Compliance Gating | Blocks risky endpoints from accessing production networks; triggers remediation workflow | Remediation workflow and exception handling verified; over-blocking rate within target |
| Guest Isolation (Internet-Only) | Prevents guest clients from reaching any internal RFC1918 address; DNS filtering applied | Firewall and DNS restriction tests confirm zero internal reachability |
| WIDS/WIPS Protection | Detects rogue APs, evil twins, deauth abuse, and mis-associations; containment where legally permitted | Simulated rogue detection drills complete within detection time target |
| Management-Plane Hardening | MFA, RBAC, secure APIs, and baseline configs protect the control and management infrastructure | Credential policy review and disabled insecure services confirmed |
| Logging, Auditing & Time Integrity | Full AAA accounting and WLAN events forwarded to SIEM with NTP-synchronized timestamps | Log completeness ≥98% and retention period verified |
| Lifecycle Operations | Firmware patching, certificate rotation, key management, and incident response runbooks | Patch SLA compliance and runbook exercises completed successfully |
Chapter Navigation
This guide is organized into twelve chapters, each addressing a distinct dimension of wireless network security design — from system components and design methods through deployment scenarios, architecture, product selection, security risk management, support integration, tools, calculators, quality acceptance, installation, and ongoing operations.