Chapter 2: Design Methods
Executable design principles, failure analysis, decision logic, and key design dimensions for wireless network security
2.1 Executable Design Principles
Effective wireless security design is grounded in a set of actionable principles that translate security policy into concrete engineering decisions. These principles are not aspirational statements but verifiable requirements, each with a defined basis and acceptance method. The following eleven principles form the foundation of this design guide and must be reflected in every configuration, architecture decision, and operational procedure.
| # | Principle | Design Basis | Verification Method |
|---|---|---|---|
| 1 | Identity-First Access — Authorize by user/device identity, not by SSID password | Security policy and audit requirements | Confirm 802.1X enforcement; test that SSID alone grants no access |
| 2 | Prefer EAP-TLS for Managed Endpoints — Certificate mutual authentication is the strongest available method | Cryptographic best practice | RADIUS config review; MDM certificate profile audit |
| 3 | Least Privilege by Role — Employees, contractors, IoT, and guests must have distinct access scopes | Risk management and breach containment | Port scan between zones; verify role-to-VLAN mapping |
| 4 | Mandatory Segmentation — WLAN users land in dedicated zones/VRFs with firewall enforcement | Breach containment and lateral movement prevention | Reachability tests between all zone pairs; firewall rule audit |
| 5 | Encrypt Everywhere — WPA3-Enterprise for air; secure tunnels for management; no legacy ciphers | Confidentiality requirements | Protocol analyzer confirms WPA3; management traffic TLS verified |
| 6 | Fail Closed — If AAA is unreachable, restrict access to minimal emergency VLAN only | Integrity and security-by-default | Simulate AAA outage; verify clients land in restricted VLAN |
| 7 | Continuous Monitoring — WIDS/WIPS + logs to SIEM with alert thresholds and response runbooks | Detection and response capability | Rogue AP drill; SIEM alert verification; log completeness report |
| 8 | Baseline Hardening — Disable insecure management, enforce MFA/RBAC, secure APIs | Platform security | Management interface audit; MFA enforcement check; API key rotation |
| 9 | Lifecycle Management — Patch SLAs, cert rotation, key lifetime policies | Operational resilience | Patch compliance dashboard; cert expiry alerting test |
| 10 | Secure Roaming — Use 802.11r carefully with EAP methods; verify PMK caching policy | Availability without weakening security | Walk test with voice application; verify no security context downgrade |
| 11 | RF Leakage Minimization — Power and channel planning reduces external signal exposure | Physical-layer risk reduction | Site survey confirms signal boundary; external measurement |
2.2 Failure Cause → Recommendation
Wireless security failures typically follow predictable patterns rooted in design shortcuts, operational gaps, or misconfigurations. The following analysis maps common failure mechanisms to their real-world consequences and provides actionable recommendations with verifiable acceptance criteria. Each recommendation is designed to be testable, not merely advisory.
| Failure Mechanism | What Actually Breaks | Recommendation | Verification |
|---|---|---|---|
| Shared PSK Reused | Password spreads across users and devices; cannot revoke individual access without disrupting all | Use 802.1X or PPSK per user/device; eliminate shared credentials | Attempt per-user revocation test; confirm others remain connected |
| Weak EAP (No Cert Validation) | MITM attack steals credentials via fake RADIUS server; users connect to evil twin | Enforce server certificate pinning and validation on all endpoints | Simulate evil twin with fake certificate; confirm clients reject it |
| Flat VLAN | Lateral movement after any single compromise; IoT or guest reaches corporate systems | Implement dynamic VLAN/ACL assignment and firewall zone enforcement | Port scan from IoT VLAN to Corp VLAN; confirm all blocked |
| No Posture Check | Infected BYOD device joins the network with full access; malware spreads | Deploy NAC with quarantine and remediation workflow for non-compliant endpoints | Connect device with EICAR test file or disabled EDR; verify quarantine |
| Logs Not Centralized | No forensic trail after incident; unable to determine scope or timeline | Implement SIEM ingestion with defined retention period and completeness checks | Log completeness report; verify all required fields present with timestamps |
| Controller Single Point | Controller failure knocks entire WLAN down; all APs lose management and policy | Deploy HA controller pair with state synchronization and redundant links | Planned failover exercise; verify APs rejoin within SLA |
| Unmanaged IoT | Default passwords and insecure services expose network; IoT becomes pivot point | Isolate IoT in dedicated VLAN, restrict egress to allowlist, monitor for anomalies | IoT egress allowlist test; confirm no direct reach to Corp servers |
| WIPS Disabled | Rogue AP persists undetected; evil twin operates for extended period | Enable WIDS/WIPS detection with locate workflow and response runbook | Rogue AP drill; confirm detection within 15-minute target |
2.3 Core Decision Logic
The design decision process follows a structured six-step methodology that transforms business requirements and device inventory into a complete security configuration. This decision logic ensures that every device class receives an appropriate authentication method, network zone, and monitoring level — preventing both over-restriction (which disrupts operations) and under-restriction (which creates security gaps).
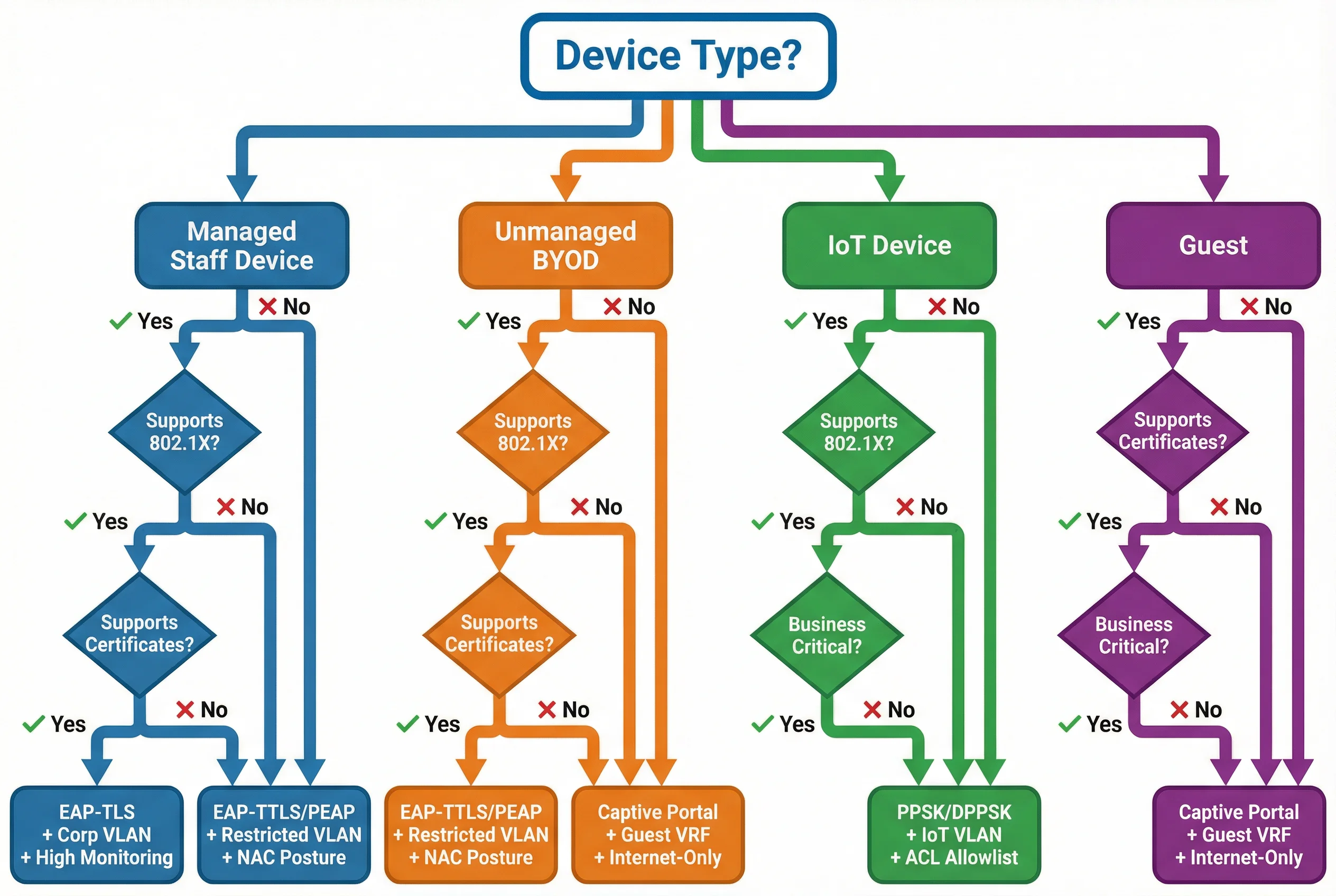
- Classify users/devices: Managed staff, unmanaged BYOD, IoT, guest — each class has different capabilities and risk profiles
- Choose authentication per class: EAP-TLS (managed), EAP-TTLS/PEAP (legacy), PPSK/DPPSK (IoT), captive portal (guest)
- Map classes to zones: Corp, IoT, Guest, Mgmt VRFs with defined east-west deny policies
- Define authorization attributes: VLAN, ACL, session timeout, posture result per role
- Define monitoring: WIPS coverage requirements, log fields, alert thresholds, retention period
- Define operations: Patch cadence, certificate rotation schedule, incident runbooks, acceptance test criteria
2.4 Key Design Dimensions
Wireless security design must balance multiple competing dimensions. Optimizing for one dimension at the expense of others creates fragile systems that fail in production. The following seven dimensions must be explicitly addressed in every design, with documented trade-off decisions where conflicts arise.
| Dimension | Key Considerations | Design Levers | Common Trade-offs |
|---|---|---|---|
| Performance / Experience | Roaming latency, airtime utilization, auth latency budget | 802.11k/v/r tuning, RADIUS caching, AP density | Security vs. roaming speed; more SSIDs vs. airtime overhead |
| Stability / Reliability | HA design, failure domains, redundancy coverage | Controller HA, RADIUS cluster, dual uplinks, UPS | Cost of redundancy vs. blast radius of single failure |
| Maintainability | Standardized templates, replaceable AP models, version control | Config-as-code, firmware orchestration, change management | Automation investment vs. manual flexibility |
| Compatibility / Expansion | Multi-vendor interoperability, Wi-Fi 7/6E readiness | Standards-based RADIUS attributes, open APIs | Vendor lock-in vs. ecosystem integration depth |
| LCC / TCO | License costs, ops staffing, refresh cycles | Cloud vs. on-prem controller, AP density optimization | Upfront cost vs. operational burden over 5-year lifecycle |
| Energy / Environment | PoE budgets, sleep scheduling, right-sized AP density | 802.3bt PoE, AP power profiles, environmental sensors | Coverage quality vs. power consumption |
| Compliance | Encryption evidence, access control audit trails, log retention | SIEM retention policies, AAA accounting, audit reports | Log volume/cost vs. retention completeness requirements |