Chapter 1: System Components
Architecture, component inventory, working principles, and operational flows for enterprise wireless security systems
1.1 System Architecture
The enterprise wireless security system is organized across three functional planes — Control, Data, and Operations — each with distinct responsibilities and interconnections. Understanding these planes and their interactions is essential for designing a system that is both secure and operationally resilient. The architecture separates authentication and policy decisions (control plane) from actual traffic forwarding (data plane), while the operations plane provides visibility, configuration management, and threat detection across both.
The control plane handles all authentication and authorization decisions: access points relay 802.1X EAP messages to the WLAN controller, which forwards them to the RADIUS cluster. RADIUS queries the identity provider (Active Directory, LDAP, or cloud IdP) and the PKI for certificate validation. Upon successful authentication, RADIUS returns authorization attributes — VLAN assignment, ACL, session timeout — back to the AP for enforcement. The data plane carries actual client traffic from APs through PoE access switches, distribution switches, and the core to the appropriate VRF zone, filtered by firewalls. The operations plane provides configuration management, firmware orchestration, log collection, and WIDS/WIPS threat detection.
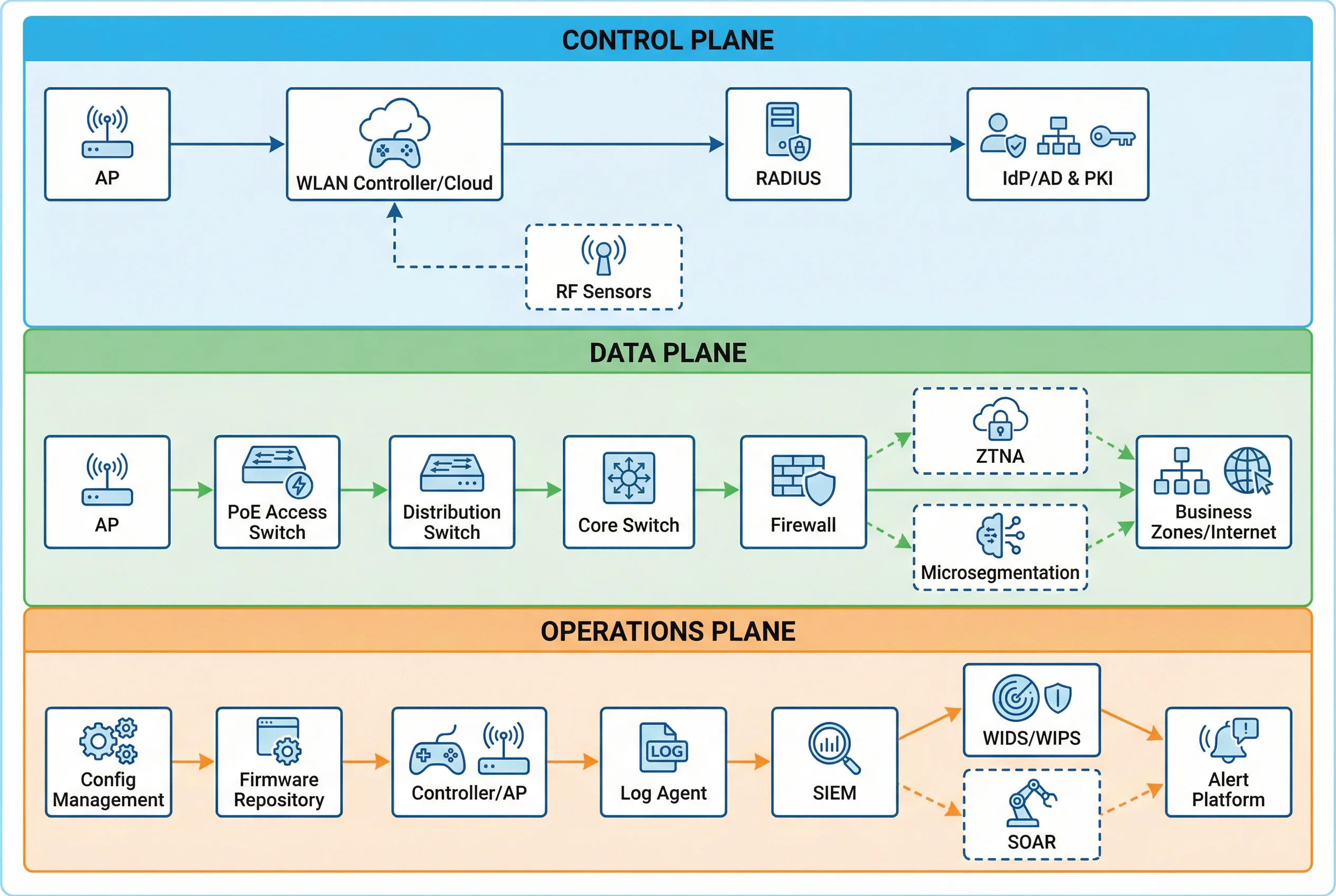
Module Relationships and Flows
Three primary flow types traverse the architecture. The authentication control flow begins when a client associates with an AP and initiates 802.1X/EAP exchange; the AP relays EAP messages to the RADIUS server, which makes a policy decision based on IdP and NAC inputs, then returns authorization attributes that the AP and controller enforce. The data flow carries authorized client traffic through the switching fabric into the appropriate VRF zone and through firewall policy to applications or the internet. The telemetry flow collects syslog and event data from controllers, APs, and RADIUS, time-synchronized via NTP, and delivers it to the SIEM for correlation and alerting.
1.2 Components and Functions
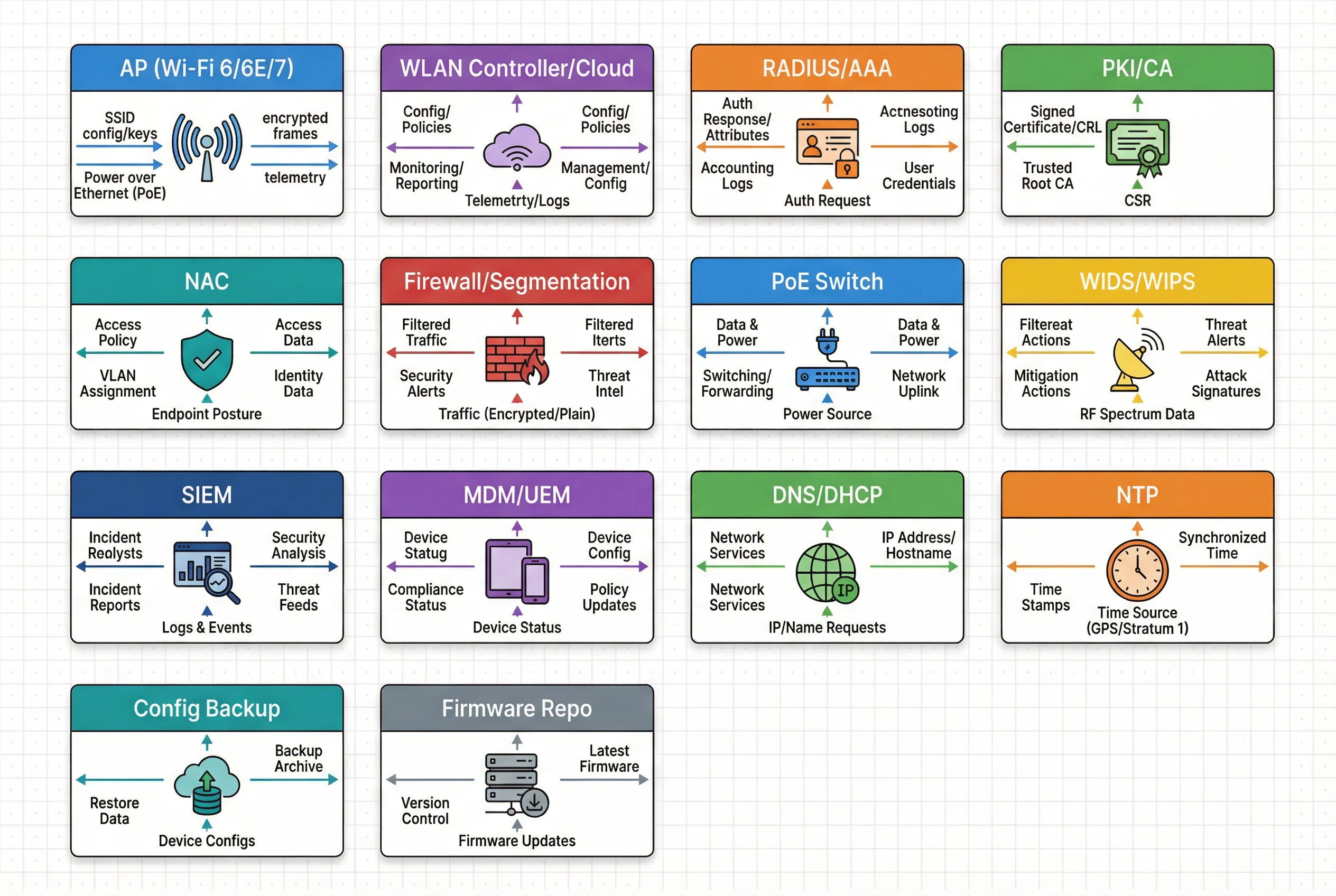
The wireless security system comprises fourteen distinct component categories, each with defined responsibilities, inputs, outputs, and key performance metrics. The component inventory below provides an engineering-grade reference for system design, procurement, and acceptance testing. Understanding the mismatch risks for each component is critical for avoiding common deployment failures.
| Component | Responsibility | Key Inputs | Key Outputs | Key Metrics | Mismatch Risks |
|---|---|---|---|---|---|
| AP (Wi-Fi 6/6E/7) | RF access, client encryption, policy enforcement at the air interface | SSID config, keys, RADIUS decisions | Encrypted WLAN frames, telemetry | Concurrent clients/AP, airtime utilization, retry rate | Underpowered AP causes high latency; weak WIPS leads to blind spots |
| Controller/Cloud | Central config, roaming management, policy distribution, firmware orchestration | Admin config, RADIUS responses | AP config, client session state, logs | Failover time, config push success rate | Single controller creates outage blast radius |
| RADIUS/AAA | 802.1X authentication, authorization, and accounting | EAP messages, IdP queries, cert validation | Accept/Reject, VLAN/ACL attributes, accounting logs | Auth latency, success rate, DB/cache health | Misconfigured EAP breaks access; weak logging harms forensics |
| PKI/CA | Certificate issuance, renewal, and revocation for devices and servers | CSR, identity proofing | Client/server certs, CRL/OCSP | Cert issuance SLA, revocation propagation time | Expired cert causes service outage; slow revocation enables compromised devices |
| NAC | Device profiling, posture checking, and quarantine enforcement | Endpoint posture, DHCP/ARP/DNS hints | Permit/quarantine roles, remediation instructions | Posture pass rate, exception volume | Over-blocking disrupts business; under-blocking allows risky endpoints |
| Firewall/Segmentation | Zone isolation, east-west traffic control, guest internet-only enforcement | Routed traffic from VRFs | Allowed/denied flows, firewall logs | Rule hit counts, latency, drop rate | Over-permissive rules enable lateral movement |
| WIDS/WIPS | Rogue AP detection, evil twin identification, deauth abuse detection | RF telemetry, sensor feeds | Alerts, containment actions | Detection time, false positive rate | Missing sensors create undetected evil twin exposure windows |
| SIEM | Central log correlation, audit trail, and security alerting | Logs from WLAN, AAA, WIPS, firewall | Correlated alerts, reports, retained logs | Ingestion completeness, retention period | Missing timestamps ruins correlation; incomplete ingestion breaks forensics |
1.3 Working Principle
Startup Sequence
System initialization follows a defined sequence to ensure all dependencies are available before client access begins. The AP boots, verifies its firmware signature against the vendor root of trust, loads the baseline configuration from local storage, and establishes a secure control channel (CAPWAP over TLS or DTLS) to the controller or cloud management platform. The controller validates the AP identity using pre-shared certificates or keys, then pushes the SSID profiles, RF plan, and WIPS settings. Concurrently, RADIUS services start with redundant nodes and verify database connectivity; PKI services confirm OCSP and CRL availability; and SIEM collectors verify log ingestion pipelines are active.
Normal Operation
During normal operation, a client associates with an AP and initiates 802.1X authentication. With EAP-TLS, the client presents a device certificate issued by the enterprise PKI; the RADIUS server validates the certificate chain, checks revocation status via OCSP or CRL, and maps the device identity to a role. The RADIUS server returns authorization attributes (VLAN, ACL, session timeout) to the AP, which enforces them immediately. For roaming clients, 802.11k/v/r mechanisms provide neighbor reports, BSS transition management, and fast BSS transition to minimize re-authentication latency while preserving the security context.
Exception Chains
| Exception | Behavior | Handling Procedure |
|---|---|---|
| Certificate Expired | RADIUS rejects EAP-TLS; clients enter authentication loop; business disruption | Alert on expiring certs at 30/14/7 days; emergency issuance; temporary EAP-TTLS fallback for managed users only; post-incident root cause analysis |
| Evil Twin AP | Clients connect to stronger rogue SSID; captive portal steals credentials; traffic intercepted | WIDS detects SSID/BSSID mismatch and signal anomalies; WIPS containment where legal; user notification; physical locate and remove; rotate compromised credentials; forensic timeline |
| Mis-segmentation | IoT VLAN reaches corporate servers due to permissive ACL; lateral movement risk | Firewall policy audit; automated verification tests; immediate block rules; validate application dependencies; implement deny-by-default east-west policy |
Recovery Procedures
Recovery from system failures relies on pre-configured redundancy and tested runbooks. Controller HA with state synchronization ensures APs can rejoin the standby controller within the defined SLA. RADIUS cluster failover behind a VIP or load balancer provides AAA continuity. Configuration backup and restore procedures enable rapid rollback of recent changes. After any recovery event, a defined acceptance test suite must be executed: authentication success verification, segmentation isolation tests, log completeness checks, and WIPS health confirmation. All recovery events must be documented in the incident register for trend analysis and preventive action.